
Why Network Engineers Still Don't Trust AI With the Network
We'll let AI write production code and draft legal contracts. Ask it to touch BGP on a core router and the room goes quiet. Here's why that instinct is correct.

Deep dives on network automation, compliance, security, and the future of configuration management, written by engineers, not marketers.

We'll let AI write production code and draft legal contracts. Ask it to touch BGP on a core router and the room goes quiet. Here's why that instinct is correct.


The network config management industry quotes scale without evidence. rConfig pulled 50,000 devices in 21 minutes on one host. Open source test bed included.

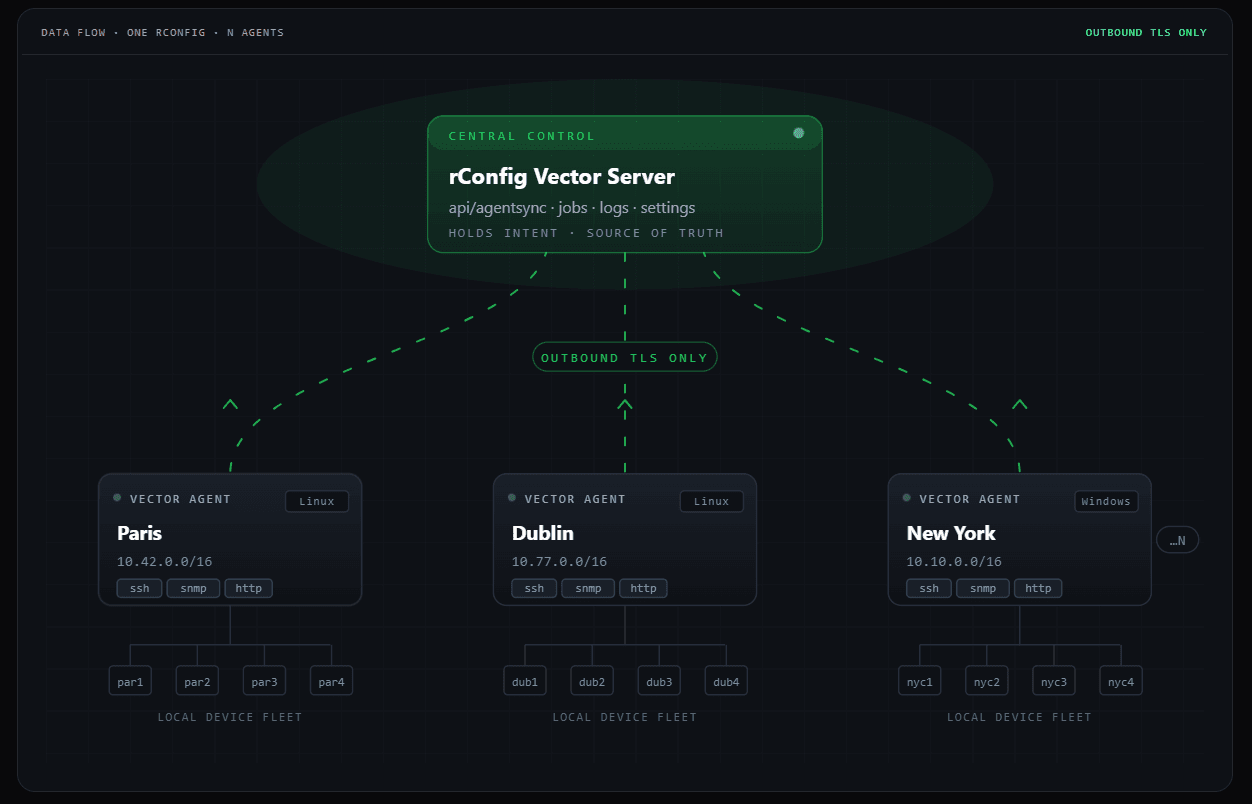
<p> Network configuration management used to be a single-instance problem. One server, one rack of devices, one team that owned them. The job was backup, diff, rollback, and an annual compliance report. </p> <p> MSPs and large operators do not have that problem. They have a fleet of customers, each with their own kit, each in a different building, each with auditors who want to see their own access list and nobody else's. The old shape of NCM does not fit that work. You cannot expose the operator console to a customer. You cannot run one collector per customer site if every collector needs an inbound firewall hole. You cannot build a per-tenant brand on top of a tool that was designed for one company. </p>
rConfig v8.2.0 is officially out, and honestly, this one has been a labour of love. It's a big release, packed with features we've been asked for, features we've wanted to ship for a while, and a handful of quality-of-life improvements that make day-to-day work in rConfig just nicer.
Learn how automated configuration auditing ensures compliance, enforces policies, and provides verifiable evidence for network security.
t starts with a concept called a configuration diff. Think of it like the "track changes" feature in a word processor, but built specifically for the syntax and logic of network device configurations. A diff tool doesn't just tell you that a file was changed; it shows you precisely what was changed, line by line. It intelligently compares two versions of a configuration file—say, the current one and the one from yesterday—and presents a clear, visual summary of the differences.
A modern NCM platform is no longer a nice-to-have utility; it is foundational infrastructure for ensuring network stability and security. Instead of wrestling with the limitations of older tools, it is time to see what a modern network configuration manager can deliver for your team.
A configuration audit trail is the tangible output of maintaining a configuration history. Think of it as a complete historical ledger for your network devices. For every change, it must answer three simple but vital questions: who made the change, what exactly was changed, and when did it happen. This level of detail is what separates a true audit trail from a simple folder of backup files. Backups are static snapshots in time. They tell you what the configuration looked like on Tuesday, but they tell you nothing about the five changes that happened between Monday and Tuesday.

Adopting modern network configuration management tools is not an operational upgrade. It is a foundational business requirement for guaranteeing uptime, enforcing security policies, and maintaining compliance in a hyper-connected world. By 2026, the idea of a traditional network perimeter has all but dissolved. Our infrastructures are a complex weave of on-premise data centers, multiple public clouds, countless IoT endpoints, and critical edge computing sites. In this environment, relying on manual configuration changes through CLI is no longer just inefficient, it's a direct threat to business continuity. We’ve all seen the post-mortems where a single typo brought down a critical service.

In 2026, a true network configuration manager provides a reliable, versioned history of every configuration across the network. It serves as the authoritative source of truth for how your network is built.

A single line of misconfigured code in a core router can trigger an outage costing millions in lost revenue and customer trust. We’ve all seen or heard the stories. In complex network environments, the only reliable safety net against such events is a systematic and verifiable network configuration backup strategy.

In any competitive market, when fierce rivals independently begin making identical strategic moves, it signals a fundamental shift in the operating environment. This is not collaboration or coincidence. It is a response to a shared, undeniable pressure that has reached a critical point. We are seeing this pattern emerge right now across the global telecommunications landscape. Multiple Tier-1 Internet Service Providers, without consulting one another, are arriving at the same architectural conclusion about how to manage their sprawling networks.
Many network teams start with what seems practical: basic backup utilities. These are often free or low-cost tools, sometimes even built into network hardware, that perform a simple task. They run on a schedule, typically using TFTP or SCP, to copy a device's running configuration to a central server. And let's be clear, having something is better than having nothing at all. That folder of dated config files feels like a safety net.

An interesting shift is happening across the networking industry in 2026. Major vendors, once champions of Network Configuration Management (NCM), are now quietly de-emphasizing or sunsetting these tools. This is not an oversight. It is a direct result of the intense focus on high-level automation and intent-based narratives, which often treat foundational configuration management as a solved problem. We are told to focus on orchestration and abstraction, assuming the underlying details will simply take care of themselves.
For the better part of two decades, the primary goal of network automation was simple: speed. We moved from a world where network changes were slow, manual, and deliberate events to one where automation could push thousands of updates in minutes. This pursuit of velocity was a success. But it also created a new class of problems that speed alone cannot solve.
Every network engineer knows the feeling. You are staring at thousands of lines of configuration code spread across a multi-vendor environment, where a single misplaced character could trigger an outage. The pressure to maintain uptime is immense, and the complexity only grows. Generative AI promises to ease this burden by streamlining diagnostics, automating compliance checks, and even suggesting remediation scripts. Yet, this promise comes with a significant catch: to be useful, the AI needs access to your network’s most sensitive data.

Nearly 800,000 Telnet servers are currently exposed to the internet, many running decade-old GNU InetUtils telnetd versions vulnerable to CVE-2026-24061 — a critical authentication bypass that allows attackers to log in as root with no password.
By 2025, the grace periods for the EU's NIS2 Directive and the Digital Operational Resilience Act (DORA) had passed, shifting the conversation from planning to proving. For CISOs, especially those in US-based multinationals with an EU footprint, this marked a fundamental change. The era of periodic, checklist-based audits is over. In its place is a new standard of continuous, evidence-based operational resilience.
As the CTO of rConfig, I’ve spent years designing tools that help network engineers automate with confidence. In that time, I’ve seen one misconception persist across the industry: that network automation and configuration management are either the same thing or mutually exclusive.

Network automation is only as reliable as the data it acts on. Scripts, workflows and orchestration engines need to know which devices exist, how they are configured, which policies apply and what impact a change will have before it is executed. This authoritative, trusted information is commonly referred to as the source of truth or system of record.
Think of network device configuration management (NDCM) as the recipe book and safety checklist for all your networking gear. It’s about tracking, controlling and updating the configurations of routers, switches, firewalls and access points so they behave the way you intend.
For decades, the management of network devices was a task left to engineers in the server room. It was a technical function, far removed from the boardroom's strategic discussions. That era is over. The U.S. Securities and Exchange Commission’s (SEC) 2023 cybersecurity disclosure rule fundamentally changed the equation, transforming network configuration from a back-office chore into a core governance function. As we explore in our discussions on modern network management, this shift requires a new level of executive attention.
The network automation landscape is evolving rapidly. Vendors are incorporating AI and machine learning, cloud-native architectures and deeper observability into their platforms. While the tooling is becoming more sophisticated, the fundamentals remain unchanged: successful automation still depends on strong configuration management, accurate inventory and policy enforcement.

For decades, scripts have been a testament to the ingenuity of network engineers. They were the original automation tool, born from necessity to tame sprawling, complex networks. We built our networks on them, and for a long time, they worked. This approach, however, has run headfirst into a wall of regulation. The arrival of the EU's NIS2 Directive and the Digital Operational Resilience Act (DORA) is not a technical debate about engineering preferences. It is a fundamental shift in legal and financial liability.

The blueprints for a bank vault are never left on a public bench. The same logic applies to the digital architecture of a modern enterprise. Your network configurations are that blueprint. They contain the collective intelligence of your operations, dictating how data flows, where defenses are placed, and how your entire digital infrastructure behaves. This collection of files is your network intelligence, a strategic asset as valuable as any physical one.
AI copilots are becoming a familiar presence in the terminal, promising to turn simple English prompts into complex network configurations in seconds. For any network engineer who has spent hours manually crafting ACLs or troubleshooting a typo in a BGP policy, the appeal is obvious. These tools can accelerate deployments and reduce the kind of small, repetitive errors that creep in during late-night changes. But this speed comes with a hidden risk, one that stems from a fundamental misunderstanding of what these AI models actually do.

Network automation promises efficiency, consistency and agility, but implementing it successfully requires more than scripts and good intentions. A sustainable automation programme needs structure, guardrails and tight integration with configuration management. This guide outlines a practical roadmap for 2026: why automation matters, how to implement it step by step, which scenarios deliver the most value, and how to anchor automation with Network Configuration Management (NCM) so you stay in control.

The conversation around AI network configuration management has shifted. It is no longer a theoretical discussion for future budget cycles but a present-day reality for technology leaders in large US enterprises. This adoption is a direct response to the sheer, unmanageable complexity of modern hybrid-cloud networks. We have all seen network diagrams that look more like abstract art than engineering blueprints. The scale of these environments, with their thousands of devices and millions of configuration lines, has simply outpaced human capacity for manual oversight.
Network automation and network configuration management (NCM) are often conflated. Many engineers assume that automating device configuration is the same as configuration management, or that one discipline can replace the other. In reality, they are two halves of the same lifecycle.

The pressure to integrate AI into network operations is immense, but early adoption is revealing hard lessons. Research from institutions like the Center for Security and Emerging Technology (CSET) shows that modern machine learning systems are “profoundly fragile” and can fail unpredictably when embedded in critical infrastructure. This isn't a distant academic concern. It's a present danger for any team rushing to bolt AI onto their network stack.
You have probably felt the frustration. You designed a brilliant automation solution, a script or workflow that could prevent critical outages, standardize hundreds of devices, and save thousands of hours of manual toil. Yet, the project is stuck. It sits in an approval queue, waiting for a signature that never seems to arrive. The common assumption is that leadership just doesn't "get it."

Aviation has achieved a remarkable level of safety through decades of discipline, procedure, and learning from every single flight. Meanwhile, many network operations teams live in a state of perpetual crisis, lurching from one outage to the next. This culture of "firefighting" is not a badge of honor. It is an expensive, exhausting, and unsustainable operational model. Uncontrolled configuration changes are a primary cause of network incidents in large enterprises, turning skilled engineers into reactive problem solvers instead of strategic architects. The constant emergencies erode morale and prevent forward progress. To escape this cycle, we must shift our perspective from reactive firefighting to proactive flight control. The principles that make air travel incredibly safe provide a powerful blueprint for building predictable and resilient operational safety networks.
In every IT department, there seems to be one: the go-to expert. This is the person who can parachute into a major outage at 2 AM and, through a combination of deep institutional knowledge and sheer force of will, bring critical systems back online. They are celebrated, rewarded, and seen as indispensable. This is the "hero engineer," a figure born not of malice but from a flawed operational model that concentrates critical knowledge in one individual.

When business leaders evaluate network automation, the conversation often defaults to a familiar place: operational efficiency. We calculate hours saved, headcount reallocated, and the incremental gains of faster deployments. While these metrics are valid, they miss the fundamental value proposition. Viewing network automation as a simple cost-saving tool is like valuing an insurance policy based on the quality of the paper it’s printed on.

Your network team tracks uptime, latency, and packet loss. Your CFO tracks EBITDA, operating margins, and risk exposure. This is the fundamental communication gap that often leaves critical infrastructure investments on the back burner. While you see a router configuration as a set of technical instructions, your finance chief sees a potential single point of failure for revenue generation.

Many IT leaders believe their networks are manually managed, holding off on automation because they fear the risk. Here’s the uncomfortable truth: your network is already automated. It’s just happening in the shadows, through a chaotic mix of ad-hoc scripts, forgotten cron jobs, and processes that exist only in the minds of a few senior engineers. This is shadow automation, and it’s far more dangerous than any formal platform.

Many IT leaders have experienced this precise moment of frustration. You walk into a budget meeting armed with a meticulously prepared proposal for network automation. You have charts showing projected efficiency gains, calculations on reduced man-hours, and a clear path to a more productive network team. Yet, the proposal is met with a polite "not this quarter." It is deferred, down-prioritized, or rejected outright. This isn't a failure of your idea. It is a failure of communication.

Discover why open-source NCM tools lacking authentication represent a critical compliance and security failure. Understand the inherent risks and learn how to select a secure solution.

For years, NetMRI had a reputation for being one of the most dependable NCM tools on the market. It wasn’t flashy, but it did the important things consistently well — and that’s why engineers trusted it. With the product now retired, it’s worth taking a closer look at what made NetMRI so popular and how modern platforms like rConfig carry those strengths forward without the overhead.

NetMRI’s end-of-life didn’t just create a gap — it exposed a bigger shift happening in the NCM space. Legacy tools that once dominated the market are now struggling to keep up with modern network realities. This article looks at why that’s happening and why many teams are moving toward lighter, faster, more adaptable NCM platforms.

Discover how a distributed architecture helps MSPs manage multi-tenant networks with greater scalability, security, and centralized control for enhanced profit.

Explore the significant cyber risks of unauthenticated network configuration management. Learn how this oversight exposes credentials and violates NIS2 and DORA compliance.

Explore why script-driven automation fails under NIS2 and DORA regulations. Learn how liability, fragility, and a lack of audit trails make a shift to governed NCM platforms essential for modern network compliance and security.

With NetMRI officially reaching end-of-life, a lot of teams are scrambling to understand what to choose next — not from a vendor marketing perspective, but from a real operational one. This guide gives you a clear, grounded framework to evaluate NetMRI replacements in 2025, based on what actually matters to network and security teams.

Discover why unmanaged network scripting has become a critical boardroom cybersecurity risk. Learn how governance failures create unauditable, fragile networks and expose executives to liability.

Explore how outdated network configuration management tools accumulate technical debt, creating significant compliance, legal, and financial liabilities under NIS2, DORA, and cyber insurance policies.

With NetMRI now retired, the network world is moving into a new phase of configuration management. Teams aren’t just looking for backups and diff reports anymore — they want real-time visibility, active verification, and deeper intelligence about the actual state of their network. This article explores how NCM is evolving and what comes next in a post-NetMRI world.

For years, network automation has been propped up by the same familiar tools and the same familiar story: a clever mix of Python...


With NetMRI officially retiring, many teams are now facing the practical reality of moving away from a tool they’ve relied on for years. Migration can feel daunting, especially when daily operations depend on accurate backups, clean compliance reporting, and stable automation. The good news is that with the right approach, the transition doesn’t need to be chaotic.

Learn how a vendor-agnostic strategy simplifies network management in multi-tenant environments, reduces operational costs, and enhances security without vendor lock-in.

For a long time, Oxidized and RANCID were the heroes of network automation. They were community-driven, lightweight, dependable, and genuinely ahead of their time. They helped thousands of organisations survive an era when vendors offered little or nothing in the way of automation or modern configuration management.


Explore the critical compliance gaps legacy NCM tools and DIY scripts create under NIS2 and DORA. Understand the specific regulatory failures in identity, traceability, and integrity.

Explore the hidden risks of using Netmiko and Jinja for network automation. Learn why your favorite Python scripts might fail a regulatory audit under NIS2 or DORA and how to build a compliant strategy.

As NetMRI reaches end-of-life, many organisations are rethinking what they actually need from a network configuration management tool. Instead of turning to heavy automation suites, teams are increasingly choosing lean, open-source–rooted platforms that are fast, modern, and easier to operate. This article explores why that shift is happening and what makes these tools so appealing in 2025.

Learn how NIS2 and DORA make network configuration a regulated control. Understand key requirements for authentication, integrity, and audit logs to ensure your tools are ready.
Script-driven network automation once helped teams move fast — but in 2025, it no longer meets compliance, security, or audit requirements. With NIS2 and DORA enforcing strict configuration governance, unauthenticated or script-based NCM introduces real organisational liability. This article explains why tools like Netmiko, NAPALM, Batfish, Oxidized, and RANCID can’t meet the new bar — and what modern, compliant network automation looks like.
Modern networks have outgrown the script-driven tools that once held them together. With regulations like NIS2 and DORA enforcing strict configuration and audit requirements, network configuration management is now a board-level issue. This article explains why scripting isn’t sustainable anymore and how secure, open-source platforms like rConfig Core v8 meet today’s compliance expectations.

Explore the strategic move away from single-vendor ecosystems. Learn how a vendor-agnostic approach enhances scalability, cuts costs, and future-proofs your IT.

Explore a detailed comparison of network automation tools. See how modern platforms move beyond simple backups to offer advanced compliance, state tracking, and scalability.

NetMRI has officially reached end-of-life in 2025. Here’s how it affects network and security teams, what risks it creates, and what a modern NCM replacement actually needs to deliver.
When engineers hear "change management," they sometimes picture bureaucratic hurdles and slow approval processes. But effective network change management is the opposite. It is not about adding red tape. It is about implementing a systematic framework that brings stability, predictability, and speed to network operations. A mature framework is built on four essential pillars that create a reliable system of record for your entire infrastructure.
The SonicWall firewall breach proves the danger of cloud-stored configuration data. Learn how rConfig’s on-prem, vendor-neutral NCM platform gives you full control of your network backups, encryption, and compliance.

The philosophy of regulatory oversight has fundamentally shifted. Auditors no longer arrive asking, "Do you have a change management policy?" Instead, the question has become far more direct: "Show me the immutable log of every change made to this firewall in the last six months." This change moves the focus from paper policies and good intentions to provable, continuous control over critical infrastructure. The burden of proof now rests squarely on the organization to demonstrate its command over its own environment.

rConfig unveils the first free in-app Generative AI and MCP AI for network configuration management, giving engineers full control of data, privacy, and insight.

Adapted and summarized from research by Barry Keepence & Mike Mannion (Napier University, 1997, IEEE).

On September 24, 2025, Cisco disclosed a serious vulnerability in the Simple Network Management Protocol (SNMP) subsystem of Cisco IOS and IOS XE software, tracked as CVE-2025-20352.

The decision to build a multi-vendor network goes beyond simple business logistics. It's often driven by specific technical requirements. For instance, an organization might rely on Cisco for its robust core campus switching, leverage Juniper for its high-performance edge routing, and deploy Fortinet for its next-generation firewall security. Each choice is optimal for its specific function, creating a powerful, specialized infrastructure. This approach delivers a significant strategic advantage, but it comes with a steep management cost.
The act of backing up a network device is passive. It’s a read-only operation that captures the state of a device at a single moment in time. Restoring, on the other hand, is an active intervention. You are writing a new set of instructions to a live piece of hardware, and the context of the network has likely changed since that backup was created. This context is everything.
The term "vendor-agnostic" is often used interchangeably with "multi-vendor," but they represent two very different concepts. Understanding the distinction is fundamental. A multi-vendor network is the common state of most enterprises, it is the problem of hardware diversity. A vendor-agnostic strategy, on the other hand, is the deliberate solution to that problem.

A new critical vulnerability (CVE-2025-20188) in Cisco IOS XE Wireless Controller Software allows unauthenticated attackers to execute commands with root privileges. With a perfect CVSS score of 10.0, this flaw demands immediate attention from network teams. This post details the vulnerability and shows how rConfig automates detection and remediation across your Catalyst 9800 devices in minutes, not days.
In high-stakes environments, from manufacturing floors to financial markets, success is measured not by raw speed but by the consistency of outcomes. A pharmaceutical company values a perfectly replicated formula over a rushed batch. A pilot prioritizes a stable flight path over record-breaking velocity. The same principle applies to modern IT, where the true value of network automation lies in its ability to deliver predictable, auditable results every time.
A comprehensive configuration history is more than just a log file; it is the single source of truth for your network's state over time. It documents the evolution of every device, from its initial deployment to its most recent modification. This historical record is a non-negotiable asset, providing immense operational and business value that extends far beyond simple troubleshooting.

We’re thrilled to share that rConfig is going Platinum at the Zabbix Summit 2025, taking place this October 8–10 in Riga. This isn’t just a sponsorship — it’s a statement. We're bringing the full power of our new rConfig V8 release to the global stage, including two major new features: a next-gen Zabbix integration and a soon-to-be-revealed AI-powered capability that’s going to change the game for network teams. If you’re in the business of automating, scaling, or securing network operations — you’ll want to see what’s coming.
Everything starts with getting the data. A robust system must automate the collection of configurations from every device on a regular schedule. This isn't just about running a single command. It means intelligently connecting to a diverse range of hardware using the appropriate protocol, whether it's modern SSH, legacy Telnet for older equipment, or even APIs for newer platforms.
For years, the conversation around network automation has been dominated by a single metric: speed. The prevailing belief was that its primary purpose was to push changes faster. This perspective, however, misses the larger strategic value that automation offers. The true measure of a mature automation strategy is not velocity but predictability. Predictability means every network change is executed consistently, can be repeated without deviation, and is fully auditable. This shift in focus moves the conversation from tactical speed to strategic stability. It aligns directly with what executive leadership truly values: mitigated risk, operational resilience, and uninterrupted business continuity. The concept is not new. In mature disciplines like manufacturing, process control has always prioritized quality and consistency over the raw speed of the assembly line. It is time for network operations to adopt the same mindset.
Misconfigurations can cripple a network faster than just about anything else. Relying on manual configuration changes and backups is both risky and resource‑intensive. Automation is the key to staying ahead of network drift and ensuring consistent, secure configurations across your environment.

rConfig’s Nautobot Device Sync integration automates device syncing, ensuring your network inventory stays accurate and up-to-date. With seamless integration and vendor-agnostic flexibility, managing devices across platforms has never been easier.
Enforcing a configuration baseline delivers strategic advantages that extend far beyond the network team. The benefits are felt across the entire business, reinforcing security, simplifying compliance, and ensuring operational stability. It shifts the network from a fragile liability to a resilient asset.

Network security teams are racing to address a new critical vulnerability in Cisco IOS XE Wireless Controller Software. With a maximum CVSS score of 10.0, CVE-2025-20188 allows unauthenticated attackers to remotely execute commands with root privileges across enterprise networks. This post explains the vulnerability details and demonstrates how rConfig's automation tools can detect, mitigate, and verify fixes across your entire infrastructure within minutes instead of days. Protect your Catalyst 9800 devices now with these step-by-step remediation techniques.
At its core, NCM is a set of processes and tools for recording the desired state of network devices, monitoring for changes and automatically rolling back or correcting misconfigurations. Leading NCM platforms provide multi-vendor configuration and change management for switches, routers and firewalls. They allow you to schedule configuration backups, track user activity and compare configuration versions so you always know who changed what and when.
Where network configuration change detection moves from being a simple IT tool to a strategic control measure. It provides the visibility and control needed to manage the integrity of your network fabric. For any leader responsible for operational resilience, understanding and implementing a proactive approach to configuration management is not just best practice; it is essential for mitigating business risk.

Discover rConfig Vector—the next-gen distributed NCM solution designed for scale, speed, and security. Built for modern IT teams, Vector offers high availability, encryption by default, lightning-fast backups, and seamless tool integration. Future-proof your network management today.

Network configuration management is the process of managing, tracking, and automating the configurations of all network devices from a central, authoritative platform. It creates a complete, versioned history of every configuration file, giving you a definitive record of your network's intended state. This is the foundation for stability, security, and compliance.

Reliable and secure network configuration is essential to the success of any business, whatever the size. See how rConfig's software ensures a safe and consistent connection.

Network downtime can cause unnecessary stress, but it can be avoided by applying proven, proactive strategies. Here, we look at how monitoring, automation and configuration backups with rConfig can prevent downtime.

Discover why opinionated network automation tools fall short in today’s multi-vendor environments. Learn how rConfig’s flexible, vendor-agnostic NCM approach empowers IT teams to automate, scale, and innovate without compromise.

Go beyond intent with rConfig’s state-aware network management. Capture real-time device behavior with state backups—BGP, routing tables, LLDP/CDP, and more—for faster troubleshooting, compliance, and full-stack visibility across your network.

As Cisco, VMware, and others pivot to AI, traditional NCM tools are being left behind. Discover how rConfig delivers modern, vendor-agnostic network configuration management—built for security, compliance, and real-world IT needs.

Relying on outdated network management tools like Rancid can expose your network to security risks, compatibility issues, and increased technical debt. Learn why upgrading to modern alternatives is crucial for maintaining secure, efficient networks.

Tired of vendor lock-in and hidden costs with closed source NCM? Discover how rConfig delivers transparency, innovation, and ROI through a secure, community-driven open source model.

Discover how rConfig helps manufacturers and critical infrastructure teams manage OT security, automate compliance, and streamline backups across IoT and industrial devices.

Discover how Laravel simplifies network automation with clean code, task scheduling, and API support. Learn best practices and real-world examples of Laravel in modern network management.

Rancid has been a staple in network management, but the time has come for a new chapter. Join us as we honor its legacy and explore the exciting future of network management with rConfig, designed for today's and tomorrow's needs.

Explore the transformative features of rConfig V7, including advanced API backup and the Script Integration Engine, designed to streamline network operations, enhance security, and boost efficiency in modern network management.

The SolarWinds breach proved closed-source secrecy isn’t security. Discover how rConfig’s open-source philosophy builds trust, transparency, and resilience in network management.

Discover how Laravel and rConfig are transforming network automation. Explore key features, real-world use cases, and the future of scalable, secure network operations.

Discover why rConfig selected Laravel as its core framework. From development speed to scalability and security, explore how Laravel powers the future of network configuration management.

Discover how rConfig V7 revolutionizes network management with API backup, Script Integration Engine, RBAC, and enhanced config change management. Experience greater flexibility, security, and efficiency for modern networks.

Explore how community drives open-source success, the challenges of sustaining contributions, and what Oxidized teaches us about project lifecycles, governance, and long-term growth.

Discover how rConfig tackled a tricky Telnet login on a legacy Avaya Switch using VT100 control codes, automation magic, and a whole lot of coffee. A win for both Core and Pro users!


Explore the pros and cons of Cisco and Juniper’s vendor-specific NCMs vs. vendor agnostic solutions. Discover how rConfig enables scalable, cost-effective, multi-vendor network configuration management.

Outdated network tools are like stale bread—useless and risky. Discover how rConfig keeps your infrastructure fresh, secure, and future-ready with modern software practices.

With VMware Smart Assurance EoS approaching, rConfig V7 offers a future-ready alternative. Leverage BYOC, automated compliance, and API-driven backups to modernize service assurance today.

Explore a side-by-side comparison of Oxidized and RANCID, two leading open-source network configuration management tools. Discover their strengths in device support, version control, and usability.

Discover how vendor-agnostic switch management software simplifies multi-vendor network environments. Learn key features, benefits, evaluation tips, and implementation best practices.

Explore top terminal emulators for Windows including SecureCRT, PuTTY, Terminus, and Windows Terminal. Compare features, security, and performance to find the ideal CLI tool for your workflow.

As the CTO of rConfig, I stand at the forefront of a transformative wave in network configuration management. Our approach to open source is not just a business strategy; it’s a philosophy that champions transparency, collaborative innovation, and ag...


Explore how Laravel simplifies network task automation through elegant tools like Eloquent ORM, task scheduling, and robust security. Learn real-world use cases and best practices.

Discover how rConfig leads the Network Configuration Management space by focusing on product excellence, value-based pricing, and customer-driven innovation—not flashy marketing or price wars.

Comply with the NIS2 Directive using rConfig. Automate risk management, enforce secure configurations, and ensure reliable network backups to boost cyber resilience and maintain essential services under EU regulations.

Critical RCE flaws in SolarWinds ARM serve as a stark reminder of the need for secure NCM tools. Discover how rConfig’s open-source model delivers resilient, community-driven security.

Learn how to install and configure Laravel with rConfig for powerful network automation. This step-by-step guide covers system prep, Laravel setup, and best practices for scaling your automation stack.

As legacy NCM tools fade and security concerns rise, rConfig V7 delivers modern, transparent, and scalable network management. Discover why the future belongs to open-source NCM.


Discover the 15-year journey of rConfig — the longest maintained open-source network configuration manager. Explore its evolution, community impact, and future innovations shaping network management.

Rancid had its moment—but your network deserves better. Discover why modern IT teams are ditching legacy tools and turning to rConfig for scalable, future-ready network management.

Explore how manufacturers can tackle OT network challenges with NCM tools like rConfig. Learn strategies for managing complexity, ensuring compliance, and embracing Industry 4.0 innovation.

Explore how rConfig is redefining NCM with intelligent automation, API-driven backups, and script integration. The future of network management is here—and it's adaptable, predictive, and developer-friendly.

With VMware Smarts facing EOL under Broadcom, explore why rConfig is the smarter NCM alternative. Compare features, security, device support, and cost to future-proof your network management strategy.
Boost NCM security and automation with SSH private key support in rConfig. Learn how to set up, assign, and troubleshoot SSH keys for safer, password-free device access—plus watch our step-by-step YouTube guide.

Still using legacy network tools? Discover why aging IT infrastructure is risky business—and how rConfig can keep your network modern, secure, and ready for anything.
rConfig CTO shares insights from 14+ years of experience on transforming network automation scripts into user-friendly, sustainable applications using design thinking and technical mastery.


Using outdated, unsupported network management software can expose your business to security vulnerabilities, inefficiency, and compliance risks. Learn why upgrading to modern solutions is essential for your network's future.

Discover Oxidized, the open-source NCM tool trusted by network pros. Learn about its origins, features, and why it still matters in modern network management.

With over 200 vulnerabilities in VMware and Broadcom NCM tools, security matters more than ever. Discover how rConfig V7 sets a new standard with transparency, rapid patching, and community-driven hardening.

Explore how Laravel streamlines network automation—from device provisioning to compliance audits. Learn practical examples, security tips, and how rConfig Automate delivers custom Laravel-based automation solutions.

Discover how integrating Digi's Industrial Cellular Routers with rConfig streamlines network configuration, enhances security, and powers global advertising networks with reliable, scalable OT connectivity.

Tired of managing network automation with raw Python scripts? Discover how Laravel, with its built-in scheduling, queues, and web UI support, offers a surprisingly elegant solution for scalable, secure network automation—even in complex environments.

Oxidized has shaped open-source network management with innovation and resilience. This article celebrates its legacy, explores the challenges of sustaining legacy projects, and calls for new maintainers to carry it forward.

Break free from vendor lock-in with rConfig’s flexible, vendor-agnostic NCM platform. Manage any device, automate API backups, and cut network costs—all while boosting security and scalability.

Say goodbye to legacy tools like Rancid and step into the future with rConfig. Discover how modern network management boosts security, agility, and performance.

Discover how rConfig is revolutionizing Network Configuration Management (NCM) in Operational Technology. Learn about its OT-specific benefits, real-world use cases, and future innovations driving security, compliance, and efficiency.

Broadcom’s VMware acquisition signals rising NCM costs. Break free from opaque licensing with rConfig’s transparent, unlimited-device pricing—built for predictable scaling and IT budget peace of mind.

Boost security, efficiency, and uptime in your smart manufacturing environment with these 10 expert tips for network configuration management. A must-read for modern factories!
Considering building your own NCM? Discover why rConfig Automate is the smarter choice—offering enterprise features, security, and flexibility without the hidden costs and risks of DIY solutions.

Explore how open source network tools like rConfig combat technical debt through up-to-date dependencies, modular design, and strategic agility—future-proofing your network infrastructure.

In the wake of high-profile breaches like SolarWinds, rConfig's CTO shares a personal reflection on trust, resilience, and how open-source NCM can secure your network’s future. Learn how rConfig puts transparency and security first.


The SolarWinds breach reshaped cybersecurity expectations. Discover how rConfig offers a transparent, secure and scalable NCM alternative built for the challenges of tomorrow, with customer trust, open-source strength and enterprise-ready resilience at its core.

Switzerland’s EMBAG law requires public sector software to be open-source, setting a global precedent. Discover the law’s impact on OSS transparency, vendor sustainability, licensing, and the future of hybrid software models.

Tired of slow, outdated NCM tools from big vendors? Discover how rConfig delivers agile, customer-focused Non-Conformance Management with faster updates, better support, and customizable features tailored for modern manufacturers.

Ditch the bloat of monolithic NCM. Discover how rConfig’s open-source, vendor-agnostic platform delivers agile updates, real-world innovation, and freedom from vendor lock-in.

Explore the current state and future of open-source network configuration management tools. Learn about the challenges, growth drivers, and innovations shaping the next generation of NCM solutions.


In the ever-evolving world of cybersecurity, outdated tools like Rancid pose serious risks. Discover why staying up-to-date with network tools like rConfig is essential for operational stability and defense against evolving threats.

Legacy Java NCMs can’t keep up with today’s networks. Discover how rConfig’s modern UI, efficient SPA architecture, and secure open-source stack deliver next-gen performance and usability.

In the wake of the SolarWinds supply chain attack, organizations are reevaluating their network tools. Discover how rConfig’s open-source approach, transparent security practices, and proactive defense make it the trusted alternative in a post-breach world.

rConfig’s open-source NCM platform champions transparency, innovation, and community-driven development. Discover how we're redefining network management beyond the VMware model.

As Broadcom reshapes VMware’s NCM roadmap, legacy tools like VOYENCE face obsolescence. Discover why rConfig offers a secure, agile alternative for the next era of network management.

Oxidized’s reliance on Ruby 3.0 presents mounting security and compatibility risks. Explore the challenges of outdated dependencies and how the open-source community can evolve while honoring the past.

Explore the key software architecture patterns driving modern network automation. From Microservices to Event-Driven Design, discover how each style enhances flexibility, scalability, and efficiency in network management.

Outdated network tools like Rancid are a thing of the past. Discover why it's time to upgrade to rConfig for a modern, secure, and efficient network management solution that’s built for today’s tech landscape.

Discover how vendor agnostic NCMS like rConfig help businesses overcome vendor lock-in, boost scalability, and streamline network operations. Future-proof your network today.

Discover how PHP and Laravel are emerging as powerful alternatives to Python in network automation. Explore best practices, clean code benefits, and sustainable, scalable development for modern NCM strategies.

In the wake of high-profile breaches like SolarWinds, rConfig doubles down on proactive security, automation, and trust. Discover how our modern NCM platform empowers businesses to build resilience, improve efficiency, and thrive in today’s digital landscape.

Discover how integrating rConfig with NetBox creates a unified Source of Truth for network management—automating configs, syncing inventory, and boosting efficiency and security.

Discover how OT network configuration boosts operational efficiency, enhances cybersecurity, and ensures scalability in modern manufacturing. A must-read for Industry 4.0 leaders.

Discover why switching from Oxidized to rConfig was like upgrading to a network automation supercar. Real-world insights, bold innovation, and a future built on fourteen years of trust.

Avoid the risks and rising costs of vendor lock-in with independent Network Configuration Management. Discover how rConfig empowers flexible, secure, and future-proof network operations.

rConfig’s CTO breaks down the real story behind technical debt in proprietary vs. open-source software—and how rConfig stays ahead with Laravel, Vue, and PatternFly. Discover our secret sauce to building future-proof, stable, and secure network automation tools.


VMware Smart Assurance is ending—don’t risk your network. Discover how to audit, plan, and migrate with rConfig V7, the future-proof NCM alternative built for compliance, cloud, and automation.

From Nmap to Traceroute, discover the top 5 command-line tools every network engineer needs for troubleshooting, security, and performance optimization. Boost your CLI skills and network efficiency.

Meet NIS2 requirements with ease using rConfig. Automate incident reporting, monitor configs in real time, and secure your network with fast detection, auditing, and recovery tools.

Technical debt may be invisible, but its impact on network management is massive. Learn how rConfig tackles outdated tools, missed opportunities, and hidden costs with a future-focused approach.


Prepare for VMware Smart Assurance End of Support with this step-by-step migration guide. Discover how rConfig V7 offers a scalable, secure, and future-ready NCM alternative.
By clicking "Accept", you agree to our use of cookies.
Learn more