Choosing the Right Network Configuration Manager: Features, Architecture, and Evaluation Criteria
In 2026, a true network configuration manager provides a reliable, versioned history of every configuration across the network. It serves as the authoritative source of truth for how your network is built.

A single line of misconfigured code can trigger a network outage costing millions. As networks grow in complexity and compliance demands intensify, manual configuration management has become an unsustainable operational risk. A modern network configuration manager is no longer a simple backup utility; it is a foundational system for stability, security, and audit readiness. This guide provides a vendor-neutral evaluation framework for CTOs and architects, cutting through marketing claims to focus on the technical and operational criteria that determine success long after a purchase order is signed.
Defining a Modern Network Configuration Manager
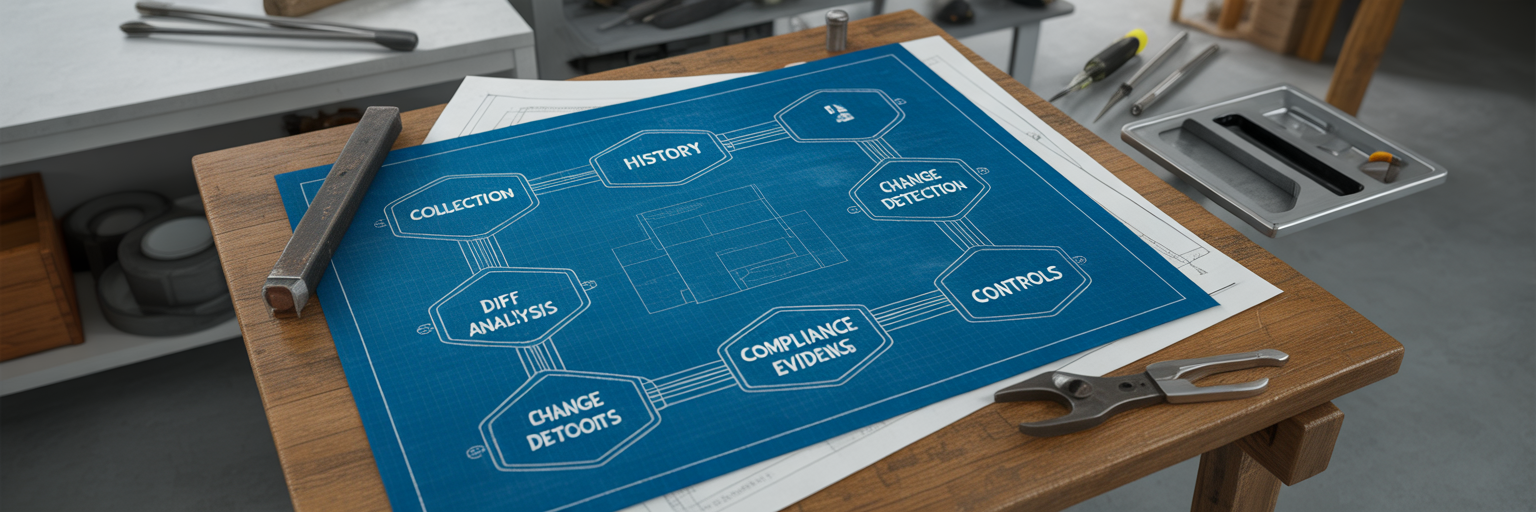
In 2026, a true network configuration manager provides a reliable, versioned history of every configuration across the network. It serves as the authoritative source of truth for how your network is built. Anything less is just a collection of scripts, not a governance platform. The minimum viable capabilities are non-negotiable: automated configuration backup, a clear version history with intuitive diffing, robust change detection, and controlled restore functions.
It is critical to distinguish this from a network monitoring system (NMS). An NMS answers the question, "Is the network up?" by tracking performance metrics like latency and packet loss. In contrast, a network configuration management software answers a more fundamental question: "Is the network configured correctly and securely?" It focuses on the authoritative state of your devices, ensuring they align with operational policies and security baselines. One tracks symptoms, the other manages the cause.
The Core Evaluation Framework for NCM Platforms
A thorough evaluation moves beyond feature lists to scrutinize how a tool performs under real-world pressure. The following criteria form a comprehensive framework for assessing any network configuration management system.
Coverage and Vendor Support
Your network is not a monoculture. A tool must handle the diverse operating systems and CLI variations from vendors like Cisco, Juniper, Arista, and Fortinet. Consider the story of a 2,000-device enterprise that realized their chosen NCM struggled with the CLI nuances of their firewall and load balancer vendors, rendering half their fleet unmanageable. True multi vendor network configuration management means the tool adapts to your environment, not the other way around.
Collection Reliability and Scheduling
Automated collection is the bedrock of any NCM. The evaluation must test how the system handles failed connections, timeouts, and complex login prompts. Does it provide clear error reporting and retry logic? Can it manage credentials securely without hardcoding them in scripts? A reliable collection process ensures your configuration history is complete and trustworthy.
Normalization and Storage Model
How a tool stores configuration data directly impacts its usefulness. Does it store raw text files, or does it normalize them into a structured format for easier searching and reporting? A long-term, indexed history is essential for forensic analysis. When an incident occurs, you need to quickly find every device with a specific misconfiguration, a task that is nearly impossible with a simple folder of backup files.
Diff/Compare and Investigation Workflows
Spotting a change is only the first step. A useful "diff" feature must clearly highlight additions, deletions, and modifications in a way that an engineer can immediately understand. The workflow should allow you to pivot directly from a change alert to the exact lines of code that were altered, who made the change, and when. This capability dramatically reduces the Mean Time to Resolution (MTTR) during an outage.
Change Detection and Alerting
Detecting unauthorized or unplanned changes is a primary function of a network change management software. Some tools rely on periodic polling, comparing the current configuration against the last known good version. Others offer realtime network change monitoring by listening for syslog messages or SNMP traps. The tradeoff is between immediacy and network load. Your choice depends on your risk tolerance and compliance requirements for detecting configuration drift.
Restore and Rollback Controls
A backup is worthless if you cannot restore it safely. A mature NCM provides guardrails around the restore process. This includes approval workflows, the ability to preview a rollback before execution, and clear version control to prevent restoring the wrong configuration. A regulated financial firm, for instance, might require a two-person approval workflow before any production configuration can be restored. This level of control is what separates a professional tool from a risky script. A proper network configuration backup software is the foundation that enables both a safe config restore and a controlled rollback with version control.
Compliance and Auditing
For any organization facing PCI, HIPAA, or SOX audits, the NCM becomes an essential evidence locker. It must generate reports that prove security baselines are enforced and provide an immutable audit trail of every configuration change. When an auditor asks for evidence of who changed a firewall rule six months ago, the NCM should provide the answer in minutes, not days of manual log correlation. This is where compliance and security auditing capabilities become indispensable.
RBAC and Authentication
Practical security means integrating with your existing identity infrastructure. The system must support enterprise identity providers like LDAP or SAML for Single Sign-On (SSO). Furthermore, Role-Based Access Control (RBAC) should be granular, allowing you to define who can view configurations, who can make changes, and who can approve restores. This prevents both accidental misconfigurations and malicious insider threats.
Integrations
An NCM does not operate in a vacuum. It must connect to the broader IT ecosystem. Key integrations include pushing data to a CMDB to enrich asset information, creating tickets in systems like ServiceNow or Jira when unauthorized changes are detected, and forwarding audit logs to a SIEM for centralized security monitoring.
Scale and Performance
The tool's architecture must support your network's scale. How does it perform with 5,000 devices or more? Does it use a distributed collection model to handle geographically dispersed sites? An MSP with clients across the country learned this the hard way when their centralized NCM collector created significant latency and polling failures for remote locations. The architecture must be able to grow with your infrastructure without becoming a bottleneck.
Security Posture of the Tool Itself
You must scrutinize the security of the management platform itself. What is its deployment model? How does the vendor handle patching and vulnerability disclosures? A vendor with a transparent security policy and a history of proactive advisories demonstrates a commitment to protecting its customers. This is not a feature you can afford to overlook.
Operational Ownership
Finally, consider who will run the tool and how it fits into your daily operations. Is it intuitive enough for the network operations team to manage, or does it require a dedicated administrator? How will its alerts and data be integrated into your incident response and change management processes? A tool that creates more operational overhead than it relieves is a failed investment.
Common Traps to Avoid in the Buying Process
Many organizations learn hard lessons after a purchase order is signed. Here are the most common traps to avoid during your evaluation.
Confusing Monitoring with Configuration Control. Network status dashboards are valuable, but they are not a substitute for governing the configuration state. Knowing a device is online says nothing about whether it is configured securely.
Prioritizing Dashboards Over Auditability. Fancy graphs are appealing, but an immutable audit trail is far more valuable. When an auditor asks for evidence of a specific change from nine months ago, a searchable, timestamped history is what matters, not a pie chart.
Blind Backups with No Restore Testing. Having thousands of backups provides a false sense of security if the restore process is untested and unreliable. Your proof-of-concept must include successfully restoring configurations to both like-for-like hardware and a test environment.
Accepting Scripts as a Governance Tool. In-house scripts lack the essential audit trails, RBAC, and safety rails of a proper network configuration management system. They are a technical solution to a governance problem and often introduce more risk than they mitigate.
Ignoring Multi-Vendor Reality. Focusing a PoC only on your primary network vendor is a classic mistake. The real test comes when you try to manage the configurations of your firewalls, load balancers, and wireless controllers. Ensure your evaluation covers the full diversity of your environment.
Key Architectural Considerations
The right architecture depends entirely on your organization's security posture, scale, and operational model. There is no single best answer, only tradeoffs.
On-Premises vs. SaaS vs. Hybrid. On-prem offers maximum control over data and is often required for air-gapped or highly regulated environments. SaaS provides faster deployment and lower operational overhead but may not meet strict data residency requirements. Hybrid models can offer a balance, keeping sensitive data on-prem while using the cloud for management.
Agent-Based vs. Agentless. Agentless is the dominant approach for network devices, using standard protocols like SSH and SNMP to communicate without installing software on each endpoint. This simplifies deployment and avoids impacting device performance. Agent-based solutions are rare in networking but can sometimes offer deeper data collection.
Centralized vs. Distributed Collection. This is a critical decision for scale. A centralized collector is simple for a single datacenter but struggles with WAN latency across multiple sites. A distributed architecture, like that offered by platforms such as Vector, places collectors closer to the devices, improving performance and resilience for geographically dispersed enterprises.
A Practical Scoring Template
To move from subjective evaluation to an objective decision, use a weighted scoring rubric. Adjust the weights below to reflect your organization's primary drivers, whether they are compliance, operational stability, or scalability.
| Criteria | Weight | Score (1-5) | Weighted Score | Notes |
|---|---|---|---|---|
| Multi-Vendor Coverage | 20% | Handles all our key vendors? | ||
| Restore & Rollback Safety | 20% | Can we trust the restore process? | ||
| Compliance & Auditability | 15% | Generates evidence for auditors? | ||
| Scalability & Architecture | 15% | Supports our distributed sites? | ||
| Integrations & API | 10% | Connects to our ITSM/SIEM? | ||
| Security & RBAC | 10% | Meets our security standards? | ||
| Ease of Use & Ownership | 10% | Is it maintainable by our team? | ||
| Total | 100% |
How a Modern NCM Aligns with This Framework
This evaluation framework is not just a theoretical exercise; it describes a category of tools purpose-built to solve these exact problems. A modern network configuration manager is designed with these criteria as its foundation. For example, reliable backups create a source of truth. That truth enables version control and diff analysis. That analysis, in turn, provides the foundation for compliance reporting and network assurance. Each capability builds on the last to create a comprehensive system for governance and stability. When you explore different network configuration management tools, you will see how they package these capabilities to meet different operational needs.
Finalizing Your Shortlist
Choosing an NCM is a strategic architectural decision about operational resilience and security. Use this framework and the scoring template to build a shortlist of two or three vendors that align with your core requirements. The final and most crucial step is a hands-on proof-of-concept. A demo is a good start, but only a trial using your own devices and workflows can provide the confidence needed for a final decision.
Why Consider rConfig
rConfig was built on a philosophy of deep focus and transparency, with open-source roots and over 15 years dedicated exclusively to network configuration management. Our approach is fundamentally vendor agnostic network configuration management, designed for the reality of complex, heterogeneous networks. We operate with a security-first mindset, reflected in our on-premises deployment model that gives you full control over your data. Our product line offers flexible options with transparent pricing models, from the free, open-source v8 Core to the enterprise-grade v8 Pro and the highly scalable Vector platform. If this guide resonates with your needs, the next step is to see it in action.
We invite you to request a personalized demo and see how rConfig aligns with your evaluation framework.
About the Author
rConfig
All at rConfig
The rConfig Team is a collective of network engineers and automation experts. We build tools that manage millions of devices worldwide, focusing on speed, compliance, and reliability.
More about rConfig TeamRead Next
Network Device Configuration Management: The Complete Guide for Multi Vendor Infrastructure
What Is Network Configuration Management (NCM)? A Complete Guide for Modern Networks